Developers recover $200,000 in crypto from compromised wallet

Share this article
A group of Brazilian developers recovered over $200,000 stolen from a victim after an exploiter got access to his wallet. After having his wallet compromised, the victim contacted public prosecutor Alexandre Senra, who then turned to the developers aiming to create a task force to recover the funds. The whole ordeal took around five months.
Afonso Dalvi, DevRel and Product Manager Innovation at Web3 startup Lumx, and also a member of the effort to recover funds, explained to Crypto Briefing that the first and hardest part was convincing the victim to share its private key.
“The hacker drained all the Ether from the wallet instantly, but there was still a significant amount of funds locked in three different DeFi [decentralized finance] applications,” said Dalvi. “It’s hard to convince someone to share the keys to their treasure, and this process took two weeks.”
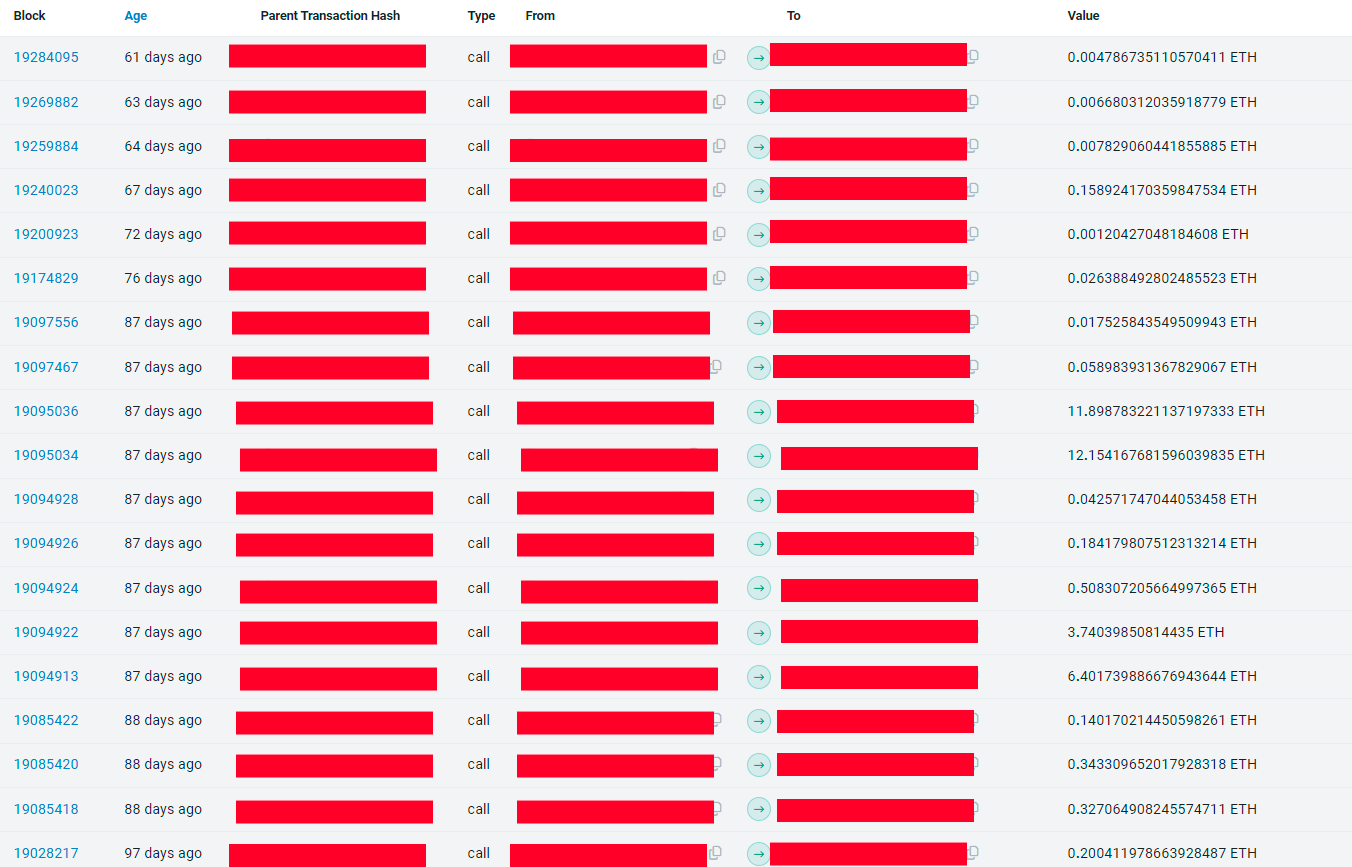
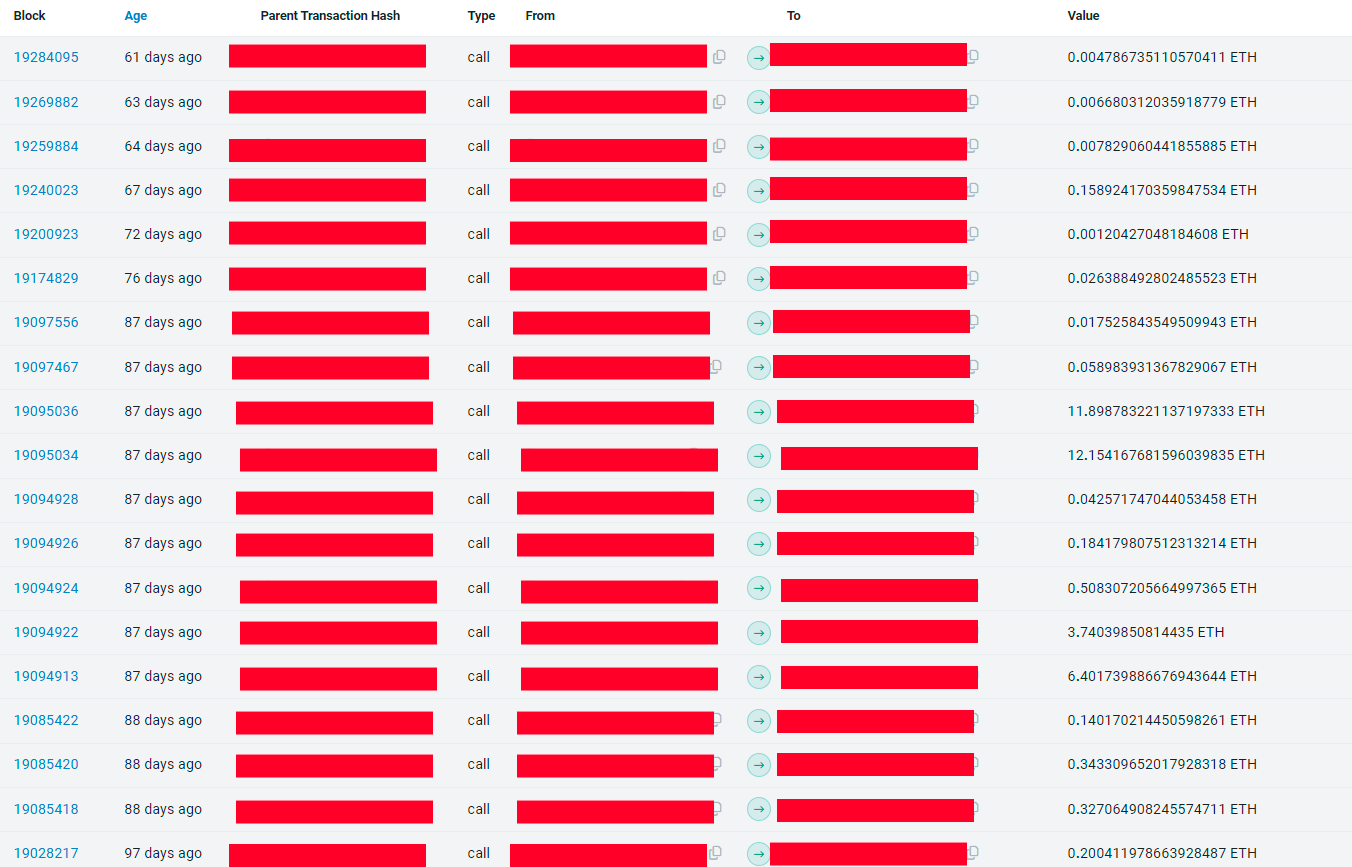
Pendle, one of the DeFi applications where part of the funds were locked, has a 54-day lock feature used by the hacker to keep the funds stuck. Therefore, a race then started to see who was going to have access to the amount after the end of the lock period. The exploiter was victorious this time.
“We developed a flashbot to do the fund capture but we did it manually the first time because we thought the hacker wasn’t experienced. Turns out he was. Then we adapted our strategy and managed to get the funds on the next unlocking events,” shared Dalvi. In the last 30 days, this exploited amassed $155,000 through ‘sandwich attacks.’
However, before they started returning the funds to the victim, Dalvi said they made sure he wasn’t, in fact, the exploiter. After confirming they weren’t doing a job for an exploiter, the developers managed to recover more funds stuck in Radiant, a money market on Arbitrum where more funds were stuck.
The last application was the staking service for the PAAL AI token, and the developers were able to get the rest of the over $200,000 stash and return it to the victim. On top of almost five months, the whole process demanded 4.4 ETH and the help of a white hat hacker who didn’t want to be identified.
Using an open-source project
Gustavo Deps and Eduardo Westphal da Cunha are two other developers working alongside Senra and Dalvi to take the funds out of the exploiter’s possession. Deps said that he used the open-source code of Flashbots, a service created to prevent maximum value extraction (MEV) cases on Ethereum, to build the bot responsible for front-running the hacker.
“We needed to send ETH to pay for the gas fees within the victim’s wallet, then use this same amount of ETH to pay for the unlock and, finally, move the funds out of the compromised wallet. Yet, it isn’t possible to do it at the same time with a regular wallet, because the three transactions must be on the same block, and a regular wallet will insert those transactions on different blocks. That’s where we used the Flashbots,” explained Deps.
Moreover, the developers used a ‘scavenging bot’, which tracked transactions sent to the victim’s wallet and took the funds before the exploiter could use them to unlock funds and move them to another address.
The scavenging bot was particularly important to capture the daily yield generated by funds locked on three different protocols, added Deps. “The applications generated around $130 every day, and the hacker always tried to take away this money.”
Despite the competition within the wallet for the funds kept in it, the developers also had to apply MEV tactics to capture the funds after unlocking them from DeFi protocols, paying fees 1,400 times more expensive than the regular fee at the time of execution.
On top of the recovered funds, there is still nearly $20,000 stuck on Radiant, which is being progressively returned to the victim. Despite being a seasoned on-chain exploiter, this time the bad agent met his match.
Share this article